mysql接続時のerror[2002]について
XAMPPを用いてApacheとmysqlを使ったWebアプリケーションを自作しているのだけれど、SQLサーバーに接続したいのに出来ない、みたいな状態になったので解決方法を記したい。ちなみに、接続できない原因は、そもそもmysqlが起動していないためであった。

原因
UbuntuでReverse Shellを取るのに手こずった件
UbuntuでJohnコマンドを使うには
Johnコマンドを用いてzipのパスワードクラックをしたかったのだけれど、単にJohnをインストールしただけでは出来なかった。そこでUbuntuでJohnを使えるようにするための手順を紹介したい。
方法
手順としては、下のコマンドを全て実行する。
git clone "https://github.com/magnumripper/JohnTheRipper.git"
ディレクトリにJohnTheRipperがあることを確認し、configureを実行する。
cd JohnTheRipper/src ./configure
ビルドする。もしエラーで止まったら、修正した後、再度実行する。
sudo make -s clean && sudo make -sj4
これでJhonを実行できる環境が整う(はず)。試しにzipファイルのパスワードを破る。以下のコマンドでzipをハッシュ値に変換し、それをhackに入れる。
/path/JohnTheRipper/run/zip2john file.zip > hack
そして、魔法をかける。
/path/JohnTheRipper/run/john --show hack
するとこのように、解析されたパスワードが表示される。(741852963の部分)

余談
そもそもエラー?が発生したり、"sudo apt install jhon"で単にJhonTheRipperをインストールしただけでは、以下のように解析結果が私の読める文字ではなかった。経験を積めば読めるようになるのかもしれない。(適当)

LINE CTF 2022 writeup
Participated the LINE CTF 2022. The 0007 article.

I did some rev challenges when the CTF started, it was too hard for me. So, I decided to see the difficulty of each problem. After 20 hours from the beginning, I took some easy problems, and I could solve one cryptography problem.
ss-puzzle

Two files containing the 32 bytes of data and one python file for encoding below were given.

#!/usr/bin/env python # -*- coding: utf-8 -*- # 64 bytes FLAG = b'LINECTF{...}' def xor(a:bytes, b:bytes) -> bytes: return bytes(i^j for i, j in zip(a, b)) S = [None]*4 R = [None]*4 Share = [None]*5 S[0] = FLAG[0:8] S[1] = FLAG[8:16] S[2] = FLAG[16:24] S[3] = FLAG[24:32] # Ideally, R should be random stream. (Not hint) R[0] = FLAG[32:40] R[1] = FLAG[40:48] R[2] = FLAG[48:56] R[3] = FLAG[56:64] Share[0] = R[0] + xor(R[1], S[3]) + xor(R[2], S[2]) + xor(R[3],S[1]) Share[1] = xor(R[0], S[0]) + R[1] + xor(R[2], S[3]) + xor(R[3],S[2]) Share[2] = xor(R[0], S[1]) + xor(R[1], S[0]) + R[2] + xor(R[3],S[3]) Share[3] = xor(R[0], S[2]) + xor(R[1], S[1]) + xor(R[2], S[0]) + R[3] Share[4] = xor(R[0], S[3]) + xor(R[1], S[2]) + xor(R[2], S[1]) + xor(R[3],S[0]) # This share is partially broken. Share[1] = Share[1][0:8] + b'\x00'*8 + Share[1][16:24] + Share[1][24:32] with open('./Share1', 'wb') as f: f.write(Share[1]) f.close() with open('./Share4', 'wb') as f: f.write(Share[4]) f.close()
We know the value of S[0] is "LINECTF{", so we can calculate a simultaneous equation for every 8 bytes in hexadecimal.
This text file is a summary of what went on in my head.
share1[ 0: 8] 25243e2a31202715
share1[ 8:16] 0000000000000000
share1[16:24] 2b0719073a0d2c2f
share1[24:32] 0214251c09404813
share4[ 0: 8] 1d08081b2d1d1231
share4[ 8:16] 0331361e3319061c
share4[16:24] 0607001b3a0f311f
share4[24:32] 3933342926756706
xor(r[0], s[0], r[0], s[3]) = xor(s[0], s[3]) = 382c36311c3d3524
xor(r[1], s[2], r[1] ) = !!!!!
xor(r[2], s[1], r[2], s[3]) = xor(s[1], s[3]) = 2d00191c00021d30
xor(r[3], s[0], r[3], s[2]) = xor(s[0], s[2]) = 3b2711352f352f15
xor(s[0], s[3], s[0], s[2]) = xor(s[3], s[2]) = 030b270433081a31
xor(s[0], s[3], s[1], s[3]) = xor(s[0], s[1]) = 152c2f2d1c3f2814
r[0] = xor(r[0], s[3]) ^ s[3]
r[1] = xor(r[1], s[2]) ^ s[2]
r[2] = xor(r[2], s[1]) ^ s[1]
r[3] = xor(r[3], s[0]) ^ s[0]
s[0] = 4c494e454354467b = LINECTF{
s[1] = 596561685f6b6e6f
s[2] = 776e5f706c61696e
s[3] = 746578745f69735f
r[0] = 696d706f7274616e
r[1] = 745f696e5f786f72
r[2] = 5f62617365645f70
r[3] = 757a7a6c6521217d
Join R to S, and Convert to a string from hexadecimal. Finally, we can get the FLAG.

OFPPT CTF 2022 writeup
This is a writeup for OFPPT-CTF 2022. The 0006 article.

This was for beginner, but I couldn't solve all of them. I found something new knowledge in rev and web challenges.
Unicode
A file with the header shown in the image below was given.

I found a string "JFIF", so I tried to fix the header in jpg format. It didn't work. This was only problem I couldn't solve in rev challenge.
Esoteric
I opened it with Ghidra.


I found "flag.txt" in line 76, and I needed to input "HELLO" to read flag. It is not simple like just input "HELLO".

In line 73, "HELLO" was compared to the STR variable. The STR variable was empty when input "HELLO", therefore it is failed. In line 40, to put a string into STR variable, we need to use sa pointer used in line 31 and 32. So, we needed to input some symbols first shown in the image below to get FLAG.

In retrospect, I think that you can get FLAG without "+" sign.
Pascal
Opened with Ghidra.

You can see the process function does something using the number from 16 to 20 in the main function.

The display_number function returns a number from 16 to 20.

In the process function, you can see that the number of the argument is compared with the input number. You can get the FLAG if all the input is correct. You need to do same thing as the C function and the f function for the input value.
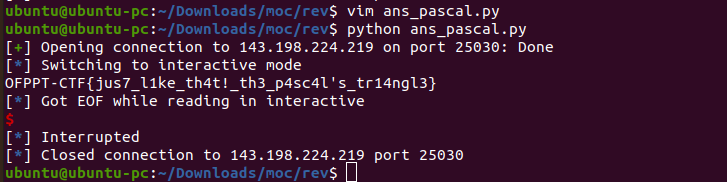
I used the pwntools. It was awesome.
from pwn import * elf = ELF("./pascal", checksec=False) host = '143.198.224.219' port = 25030 def func2(num): tmp = 1 for j in range(num): tmp *= num - j return tmp def func1(num, i): return int(func2(num) / (func2(i) * func2(num - i))) r = remote(host, port) # receice a random number now = r.recvline() a = now.decode('utf-8') for i in range(int(a) + 1): r.sendline(str(func1(int(a), i)).encode()) r.interactive()
FInally, you can get the FLAG.
Decompile
Opened with Ghidra for the first step.

This program is similar to the Pascal. You can see that the ivar3 variable is compared with the input number in line 37.

In the function1, it calculates the greatest common divisor of local_20 variable and local_28 variable.

In the function2, it calculates the factorial of the ivar3 variable plus 3.
The solution is below.
import math from pwn import * elf = ELF("./decompile", checksec=False) host = '143.198.224.219' port = 21530 def func1(num1, num2): return math.gcd(num1, num2) def func2(num): if (num == 0): return 1 else: return func2(num-1) * num r = remote(host, port) while (True): # receive two numbers now = r.recvline() if (b"fun() took" in now): break a, b = map(str, now.decode('utf-8').split()) # send number which does func1 and func2 num = func2(func1(int(a), int(b))+3) r.sendline(str(num).encode()) print(now.decode('utf-8')) r.interactive()
You can get the FLAG.

Trickster
I was surprised that the game could be working with Python. This program is using library called pygame.

This game begin with the image like this.

You need to avoid the Grim Reaper.

If you bump into it, you will failed.

For me, I fixed the program not to bump into the Grim Reaper. The FLAG will be shown over 100 dodge.
php
Index.php was given.

I thought that I needed to calculate for a number would result in the same hash value (=Collision). However, I found there are two equal signs and three equal signs in the php comparison operator. In the case of two equal signs, a hash value begin with "0e" is computed as a power of zero. So, it will be true if the hash value of input number begin with "0e".
Now, You can find the correct input with the program below.
import string import hashlib strings = string.ascii_uppercase + string.ascii_lowercase + string.digits def check(h): if (h[:2] != "0e"): return 0 for i in range(2, len(h)): if (h[i] not in string.digits): return 0 return 1 def make_magic(moji, cnt): h = hashlib.sha1(moji.encode()).hexdigest() if (check(h)): print(moji) if (cnt == 9): return for j in strings: moji += j make_magic(moji, cnt+1) moji = moji[:-1] moji = "" for i in strings: moji += i make_magic(moji, 0) moji = ""
I input a string "AAAAABzIOf" and got the FLAG.





